Visiting the Dark Web isn’t illegal in itself, but it is illegal to engage in illicit activity...
Credentials of many online services which include banking, telco, social media networks and many more are being...
Sections of the dark web are often closed down too, as part of police operations. DuckDuckGo is...
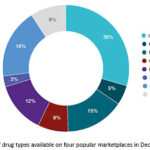
This market also features an ‘Other’ section where users can browse delivery services, as well as bank/SIM...
That groundwork was the basis for the Tor Project, which was released in 2002 and launched a...
If top-notch privacy is your goal, yes, you can use the Tor Browser for all of your...
It also hides your real IP address from Tor’s entry node, which is the first hop in...
There are many different ways to access the dark web, but navigating it can be tricky and...
Some of these sites can be found through regular web browsers, but you’ll then need to switch...
You don’t even need to use Tor Browser, but keep in mind other browsers can still pass...