If so, you could end up on the darknet even though you’re not a drug lord. The dark web is a constantly evolving landscape, shaped by technological advancements and evolving strategies of law enforcement. As technology continues to advance, new tools and techniques may emerge that could either enhance or hinder the anonymity and accessibility of the dark web. For example, advancements in artificial intelligence and machine learning could enable law enforcement to more effectively analyze vast amounts of data and identify patterns of criminal activity within the dark web.
The People And Nature Blog
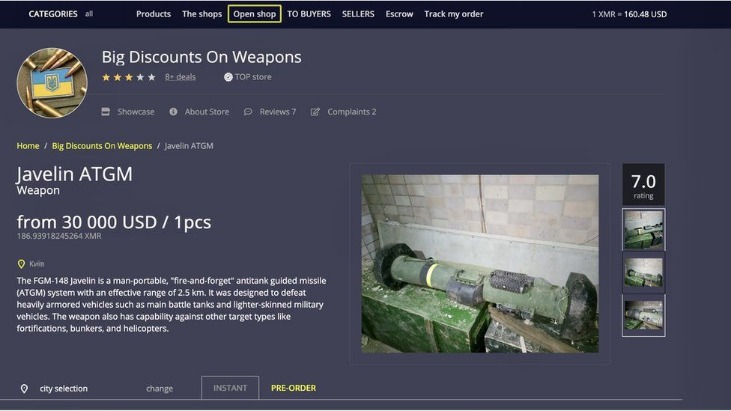
Remember that any website engaging in illegal activities such as drug trafficking, weapons sales, hacking, and human trafficking violates international laws and, therefore, is illegal. All websites on the open web can be accessed through standard web browsers such as Firefox, Internet Explorer, and Google Chrome. These publicly available websites are labeled with registry operators such as “.com” and “.org.” The websites are easily found because search engines can index the web through visible links.

Although there are many hypotheses, nobody can be certain about these numbers. Surprisingly, the tiniest portion of the web is typically the most popular and accessible. While the Dark Web hosts illegal activities, it also supports legitimate uses like protecting free speech and aiding cybersecurity. A person must exercise caution while accessing the Dark Web, while being mindful of legal obligations and possessing an ethical perspective.
Understanding And Mitigating The Risks Of Mobile And Remote Work Cybersecurity
The UK and the US have strong legal frameworks regarding data breaches because data leaks constitute severe incidents. GDPR violations in the UK can lead to maximum fines that reach either £17.5 million or 4% of the organization’s global annual turnover. The U.S. Data Breach Notification Laws mandate rapid breach reporting from companies while HIPAA and similar regulations enforce healthcare organizations to pay fines reaching up to $1.5 million for each recorded violation. Analyze traffic patterns to detect anomalies indicative of exit node poisoning.
The dark web, a shadowy realm within the vast expanse of the internet, remains largely hidden from the prying eyes of conventional search engines. Unlike the surface web, which is readily accessible to anyone with an internet connection, the dark web requires specialized browsers and specific knowledge to navigate. While the Dark Web hosts legal and legitimate content, such as privacy-focused forums and whistleblower platforms. But, it is also known for the notorious illegal activities like black market for drugs, selling of stolen data, and hacking services. The dark web poses significant cybersecurity threats to both individuals and businesses.
So How Can I Get Hit By Malware?
The anonymity provided by Tor and other privacy-enhancing technologies makes it difficult to trace the activities of individuals and groups operating within this hidden corner of the internet. Furthermore, the vastness of the dark web, with its countless websites and forums, complicates the task of identifying and tracking potential criminal activity. Webz aids in preventing cyberattacks by offering Dark Web Data Feeds, bolstering your cybersecurity intelligence capabilities. Webz Dark Web Data API encompasses an extensive range of sources, including millions of deep, dark, and open web sites, forums, marketplaces, paste sites, and more. This comprehensive coverage empowers your cybersecurity solution to stay vigilant, monitor potential threats, and proactively defend against malicious activities originating from the depths of the internet.
Tor and I2P are the two commonly used tools for accessing the dark web to provide anonymity. Another website is Dread, which is often called the “Reddit of the Dark Web.” It’s a community platform where users can discuss new markets, share onion links, add reviews, and much more. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal.
Tor websites are located at this far end of the deep web, which are deemed the “dark web” and are only accessible by an anonymous browser. The Internet is sizable with millions of web pages, databases, and servers all run 24 hours a day. But the so-called “visible” Internet (aka surface web or open web) — sites that can be found using search engines like Google and Yahoo — is just the tip of the iceberg. For a local machine configuration, he recommends a computer purchased for cash running Linux, using a local Tor transparent proxy. For operations security he suggests avoiding storing conversation logs, varying writing styles, avoiding mobile phone-based tracking and leaking false personal details to further obfuscate one’s identity. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor….

Get Cybersecurity News, Insights, & Intelligence Straight To Your Inbox
The dark web intelligence market experiences a dynamic increase in cybercriminal operations. 4iQ reported that stolen account credentials on the dark web experienced an 82% increase in 2022 to reach 15 billion. Identity theft cases lead the dark web monitoring activities at 65% while credit card fraud follows closely behind at 15% and the number of card dumps exceeds 192 million according to Sixgill’s reports. Chainalysis researchx` Anatomy reveals dark web cryptocurrency activity almost doubled between 2020 and reached $25 billion in 2022 thus underscoring the necessity for advanced tracking systems. The Dark Web is a breeding ground for cybercrime, with many websites hosting malicious software, phishing scams, and other types of malware.
Watch Out; Your ISP Could See You Using The Tor
Additionally, NordVPN offers a DoubleVPN option that lets you use the Tor browser with two VPN connections simultaneously, which may reduce your internet speed. A VPN encrypts your web traffic to ensure it’s hidden from the big brother who could be watching you online. You’ll find the more dangerous content and activity at the dark end of the deep web. This is where Tor websites are located, deemed the ‘dark web,’ and can only be accessed by an anonymous browser. While much of the content on the deep web is harmless, users can accidentally access dangerous content by navigating through tangential pathways, leading them to piracy sites, radical forums, or violent content.
Popular Right Now
To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. The only difference is that it passes your traffic through random nodes before reaching the destination. This means your activities cannot be traced or your browser history exposed.
- Though people usually think of dark websites as the wrong online place, that’s not the complete truth.
- It also keeps the graphical copy and text of the page for better accuracy.
- Let’s unpack both of these concepts in terms of the “dark web browser” and the websites themselves.
- Another is the Invisible Internet Project (I2P), which specializes in the anonymous hosting of websites on the dark web.
Unmasking The Dark Web: How UAE Businesses Can Protect Their Digital Assets
However, it’s illegal if you venture into the dark web to commit unlawful actions such as downloading child porn, buying fake documents, drugs, credits card, and more. Information on the dark web is not meant for public consumption, and the dark web protects personal data intended to be private. The dark web is rife with cybercriminals who offer their services either as individuals or as part of a group.
Websites are usually labeled with registry operators like “.com” and “.org” and can be easily located with popular search engines. The dark web is a common gathering place for hackers and other cybercriminals, which can make browsing the dark web a risky activity. Visitors to the dark web should exercise extreme caution when downloading files, as they may infect your devices with viruses, malware, trojans, ransomware, or other malicious files.
Dark Web, Not Dark Alley: Why Drug Sellers See The Internet As A Lucrative Safe Haven
Stay updated on the latest threats and ensure your data remains secure by leveraging these advanced solutions like Lunar. These RATs are often sold on dark web forums and are frequently bundled with other malware as part of larger attacks. Faison was arrested and charged this month with attempting to acquire a chemical weapon. It means unless you use a VPN that encrypts your internet traffic, they always receive all information about you and your digital life.