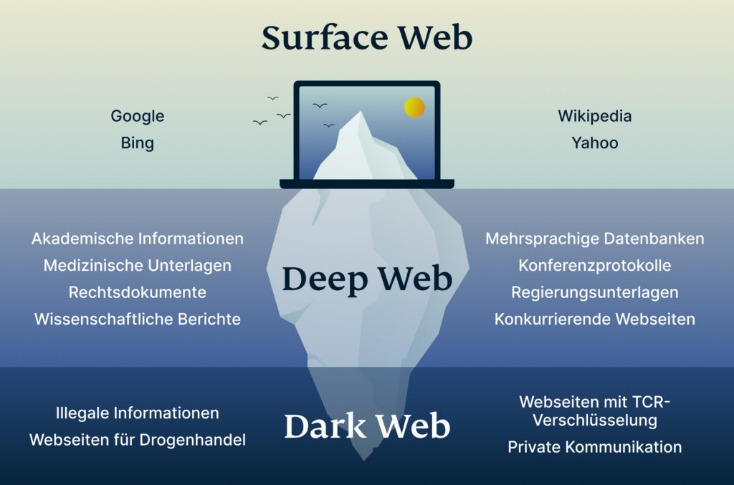
This article will delve into the disparities between Illicit Telegram Channels and Dark Web Forums, shedding light on their distinct characteristics and functionalities. By doing so, readers will gain a better understanding of the unique aspects of these platforms and their implications in the realm of cybercrime. Please note that the site is automatically filled from open sources and does not store information about Telegram channels except for the name, description, link, and avatar. If you come across a Telegram channel that violates the law, please contact us using the contacts listed in the site menu. After reviewing the complaint, we will remove this Telegram channel from the search. For the search, you can select the category you are interested in or enter your query in the search bar.
Illicit Telegram Groups Offer Hardened Operations
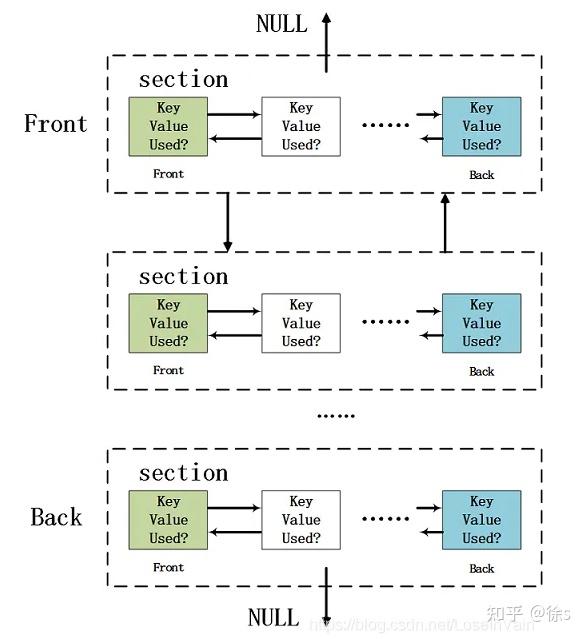
Unfortunately, the Telegram API only allows channel administrators to view the list of followers, a limitation we faced. This restriction makes it difficult to determine whether the same users are interacting in multiple channels within a single CAC or across different CACs. Using the two tools, found 1,210 files to be malicious, out of which only 491 (4̃0%) had been priorly scanned by Hybrid Analysis, suggesting several of the malicious files shared in the CACs had not been seen by the tool. Considering Hybrid Analysis is a popular tool which contributes threat intelligence to antivirus vendors, there is a possible detection gap for these files. We cross-referenced the APKs with those listed in the AndroZoo repository (Allix et al., 2016), using package names to avoid discrepancies caused by modified file hashes. Interestingly, we found that 83 of the malicious APKs had corresponding entires available on the Google Play Store indicating Telegram’s role in distributing repackaged or potentially malicious apps.
- Within weeks, Hydra-branded channels appeared offering drugs, stolen data, and counterfeit documents.
- Telegram’s approach to privacy and moderation presents substantial challenges for managing illegal content and collaborating with law enforcement.
- Gathering threat intelligence on how cybercriminals operate is one of the most effective ways of ensuring that your security matches the most up-to-date attack techniques.
- While Telegram remains a critical hub for cybercriminal activities, it is just one part of the larger dark web ecosystem where threat actors exchange stolen data, hacking tools, and illicit services.
- The torch passed to dedicated darknet forums, often on the Tor network, which allowed marketplaces and vendor reputation systems to emerge.
Top 6 Dark Web Telegram Groups And Channels
Expect cybercriminals to split their operations between messaging apps and traditional underground forums and marketplaces. Comprehensive monitoring requires coverage of both the dark web and messaging apps. We see many of the same threats on Illicit Telegram channels that we see on dedicated dark web markets and forums. In many cases threat actors have moved directly off of more traditional TOR websites, and onto Telegrams offering the exact same goods and services. Although cybercriminals mostly use a combination of messaging apps, Flare’s research shows that as of January 2025, Telegram is still the most-used communication tool among threat actors.

Although its Telegram channel was previously taken down due to policy changes, the group has successfully reestablished its presence and continues its operations. By leveraging this intelligence, organizations can proactively secure accounts, enforce password resets, and prevent unauthorized access attempts before they escalate into full-scale breaches. Karenza Moore, an expert on club drugs at Newcastle University, said neither banning drugs nor seizing them had much impact on the public’s ability to buy them. Authorities hope that big drug seizures will have a knock-on effect on supply, in turn increasing the price of drugs.
Data Leak Monitoring: A Radar For Breaches And Cyberattacks
That’s why companies and organizations must remain vigilant about these underground networks, as a data breach or financial fraud can begin with a simple conversation on Telegram. The platform soon became a key node in the Dark Web ecosystem, where malicious actors found the perfect environment to operate with a certain degree of anonymity. To save some time and effort, consider using NordStellar — a cyber threat monitoring and threat exposure management solution. NordStellar helps companies safeguard against cyber risks by thoroughly evaluating external attack surfaces. In addition, the service provides dark web monitoring tools, capable of detecting leaked credentials and other sensitive information the moment they appear on the dark web. Telegram is a widely used messaging platform that has also become a meeting point for clandestine activities.
Track Both Dark Web Forums And Telegram For Greater Protection
Consequently, this aids in preventing various illegal activities, including drug trafficking, identity theft, and online fraud. Hacker groups, underground markets, and ransomware networks began using Telegram to distribute stolen data, sell hacking tools, and coordinate illicit operations. For a long time, the lack of strict moderation allowed these communities to grow unchecked, turning the app into an extension of Dark Web forums.
Thematic Analysis Of Replies
The platform’s features, such as encrypted communication and anonymous group interactions, provide a convenient and secure tool for managing cybercriminal operations. This aspect aligns with the broader trend of digital platforms serving as enablers for cybercrime, reflecting the dark web’s function in the digital landscape. Telegram has become a key tool for cybercriminals thanks to its massive group capabilities, encryption features, and user anonymity. Many of these channels operate almost like Dark Web forums, facilitating the exchange of stolen data, hacking tools, and all kinds of illegal services.

Wolfonaire Premium Signals 🚀 🚀 🚀 🚀 Telegram Channel
This knowledge enables them to fortify their defenses against potential attacks, thereby reducing the risk of data breaches. It also allows organisations to proactively detect security vulnerabilities and mitigate them before they are exploited. The activities within illicit communities on Telegram and dark web forums differ significantly when it comes to the buying, selling, or trading of cyberattack methods.
MOST POPULAR CHANNELS
- For the search, you can select the category you are interested in or enter your query in the search bar.
- That’s why companies and organizations must remain vigilant about these underground networks, as a data breach or financial fraud can begin with a simple conversation on Telegram.
- Telegram is a popular messaging app, known for its secure and encrypted communication features.
- These features attracted privacy-conscious users but also made it appealing to individuals engaging in illicit activities.
- Submit your Telegram channels and groups to Telegram directory, instructions given at the bottom of this page.
For example, rarely has it been seen that the illicit communities on Telegram allow others to buy, sell, or trade other cyberattack methods such RaaS or other attacks as a service. This is often done ahead of time before law enforcement intervenes to shut down the group or the Telegram channel has been reported and threatened to be shut down due to illicit activity. Many of the groups researched commonly offered either user data or services geared toward being able to aid in an attack of an organization. In this sense Telegram actors tend to be more focused on providing the means to gain access to a system rather than the access itself. It can be pretty easy for a Telegram user like you to stumble into a channel or group with crypto scams, for example.

Because of this risk, some sources have even labeled the app as a destination for cybercriminals1. And although Telegram’s owners have taken measures to limit the number of cyber threats (for example, by eliminating some of the Chinese cybercrime markets2) the risks seem to persist. Encryption is an interesting topic when it comes to illicit cybercriminal activity. Telegram offers end-to-end encryption for messages by default, which helps to avoid potential man-in-the-middle attacks that can snoop on messages in transit.
However, once they are accepted, these users can trade and purchase illicit drugs, including cocaine, MDMA, and methamphetamines. Even if you don’t get in trouble with the law, paying for substances via a credit card or bank transfer could bite you in the backside if a group member doesn’t deliver your goods or uses your details to commit fraud. To receive notifications about new content, users on Telegram must follow (join) a specific channel. We tracked the growth of followers across all CACs in our database over the study period, yielding insights into their growth patterns. Collectively, the identified CACs are followed by approximately 23.8 million users, with a median of 8,000 followers per channel.
To mitigate the risks posed by exposed credentials, organizations must actively monitor and respond to identity-related threats. SOCRadar’s Identity & Access Intelligence module enables security teams to detect compromised credentials across various dark web sources, including stealer logs, data breaches, and underground Telegram channels. The dark web has been notoriously known as the corner of the internet accessible through TOR, and home to nefarious activity. Within the dark web also sits many forums that allow others to share, communicate, buy, sell, and trade illegal goods and services regularly.