This issue affects not only Tor but also the I2P and Freenet anonymity networks; in a 2022 investigation, a Freenet content analysis revealed that 12.0% of the 7161 analysed freesites contained CSAM16. The first systematic analysis in 2013 indicated that 17.6% (206 of 1171) of the onion services surveyed shared CSAM and concluded ‘The support for the further development of Tor hidden services should hence stop1’. Measurements on onion service visits find CSAM sites to be the most popular ones17. In 2014, an estimated 17% of the onion websites provided sexual material, of which about half was CSAM18. Overall, we have a growing understanding of the environment of these darknet forums on a technical and community level.

The Psychology Of Darknet CSAM Forum Members
With this said, I would be interested in building a list of reliable link sites that can be endorsed in the long term. Users, who could view videos and upload their own, paid for the service with hard-to-trace bitcoin. Users earned “points” by uploading their own porn images and videos. At least 23 young victims abused by the site’s users were rescued in the USA, Spain and the United Kingdom. The Department of Justice said two users of the site died by suicide after the execution of search warrants.
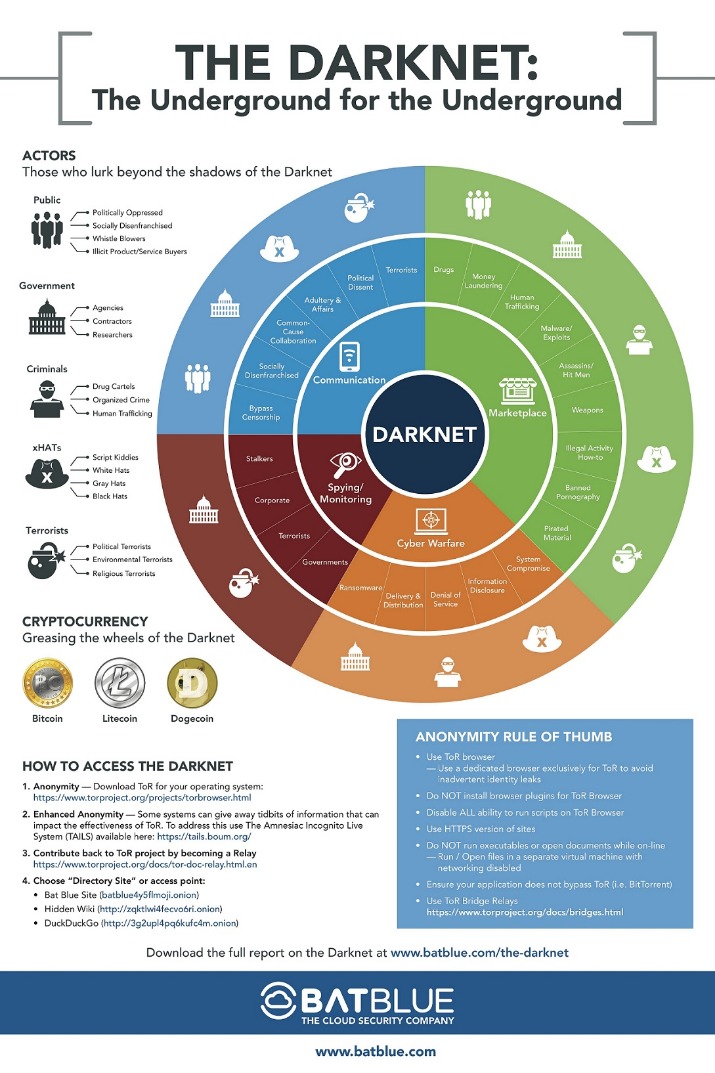
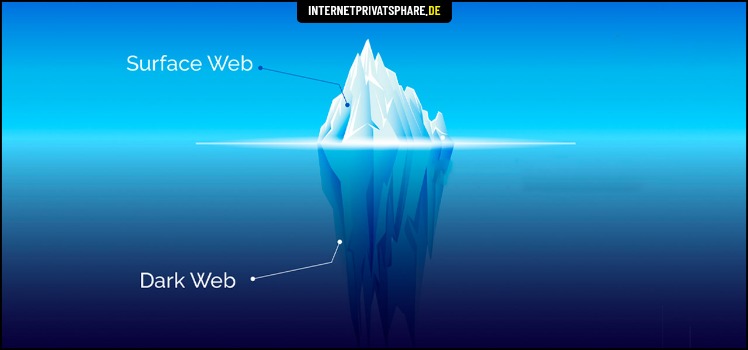
If you do need to access a dark web website for legitimate reasons, you can check directories like The Hidden Wiki to help find options. Dark web marketplaces are websites where you can exchange illicit goods and services like stolen credit cards, account login credentials, counterfeit items, drugs, and other items. Usually dark web transactions are made with Bitcoin or other cryptocurrencies. There are thousands of websites on the dark web, many—but not all—of which are illicit marketplaces selling stolen personal data. Learn more about the kinds of sites that can be found on the dark web and how you can access them. Then, try LifeLock free for 30 days to help find out if your personal data is leaked on the dark web.

FAQs About The Dark Web And The Websites That Live On It
Your search activity isn’t stored, and you get decent answers for most queries without all the tracking. The search engine is also available on the dark web and offers an additional layer of anonymity and privacy with fast search results. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Even if you’re using a private, anonymized crypto wallet, there are other ways your identity can be revealed—even if it’s something as simple as letting a personal detail slip in an instant message.

Use The Tor Browser
For example, you can find information unavailable to the public and share data privately while protecting your online identity. Note that most dark web transactions are carried out using Bitcoin or other cryptocurrencies. When using Tor without a VPN, each volunteer-operated node that your traffic passes through can potentially see some of your data. While Tor anonymizes your location, the exit node—the final point before your data reaches its destination—can view unencrypted information, such as the websites you’re visiting or data you’re transmitting.
- Although profiting from pirated copyrighted material is unethical and illegal, there are some exceptions to using copyrighted material, such as a “private study” provision under UK law.
- But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple.
- Hackers, journalists, and security companies use this hidden corner to exchange information and gather intelligence that’s not accessible through the regular internet.
- But online and at your finger tips, if you can make it past the surface web.
- They worked as administrators of the site and gave advice to members on how to evade law enforcement when using the platform for illegal child pornography.
More Security Articles
The Guardian Tor site is a mirror of its regular Tor site, offering the same news, analysis, and opinion as its regular web portal. The only way to access Tor sites that the Tor Project recommends is to use Tor Browser(new window), a modified version of Firefox that routes all connections through the Tor network by default. Tor was originally an acronym for The Onion Router, which references Tor’s multiple layers of security. Onion Services are websites that exist within the Tor network and can only be accessed from the Tor network.
Exploring Dark Web Forums
This enables the CSAM community to understand the consequences of the LEA operation. However, as the members realize that they are not subject to investigation—e.g., their residence has not been searched under an LEA warrant—they quickly communicate with friends and members of the community. They discuss an online rendezvous point, where they either join or re-engage with another active CSAM darknet forum. The darknet, in simple terms, is a network available on the Internet.

Platforms like SecureDrop allow these carriers of truth to evade tracking. It protects their submissions using high-end encryption and doesn’t log their IP addresses or device information – full anonymity. It is important to note that the people or journalists who use ProPublica to spread their truth recognize the risk of doing so. As a result, we want you to stay safe and anonymous by using a paid VPN service whenever you surf this dark web platform.
Why Is Tor So Slow?
It can only interact with the gateway, the most effective method by which the browser protects user applications from learning a device’s IP address. While accessing the dark web using Mozilla Firefox is possible, you must first adjust its settings. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. Initially, the dark web was mainly used by government agencies, big businesses, hackers, and cybercriminals. However, technological advancements such as encryption and privacy-focused browsers like Tor enabled the general public to access it. Some whistleblowers and journalists use these portals to safely leak information, especially when a source requires complete privacy.
If you spend most of your time online (who doesn’t, really?), you might have come across the term dark web before. The mystery surrounding it creates a lot of curiosity among people and the chances are that you’re one of them as well. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing.
Within darknet CSAM forums, articles and videos about the operation were critically analyzed, resulting in an update of security advice from forum administrators. The TOR browser, on its own merits, is an application and preforms as an Internet browser, enabling the user to access the world wide web, while ensuring anonymity for the end user. In addition to these “clearweb” sites, the TOR browser accommodates darknet sites or onion sites—websites whose url ends with .onion. These darknet sites are websites, forums, and other online archives that are not indexed by publicly recognized search engines, referred to as “hidden services” or HSes.
You won’t find any “hidden” stories here—it’s the same content as the normal web edition—but users in countries with government censorship will appreciate having a secure way to access it. The dark web also helps individuals communicate about or sell illegal items such as weapons, drugs, malware, etc. Many people see hacked information and stolen card data being sold on the dark web.