Volunteers compile the list of links by hand, thus creating a high-quality index of deep web content across dozens of categories. There is no official data available, but most experts agree that the invisible web is several times larger than the visible web. The true size of the internet is unknown, and the same goes for the invisible web. However, the invisible web can be roughly divided into the deep web and the dark web.
Exploring the dark web requires specialized knowledge and tools due to its anonymous nature and the use of encryption to maintain user privacy. It’s important to note that while the dark web can be used for legitimate purposes, such as protecting the privacy of activists and journalists, it can also host illegal activities. Therefore, caution and awareness of legal implications are paramount when accessing it. Dark web search engines are specialized tools that allow users to perform web searches within the dark and deep web. Unlike traditional search engines like Google or Bing, these tools operate on the Tor network — a hidden ecosystem where most content is intentionally obscured from public view. Instead of browsing indexed links, dark web engines scour encrypted, often anonymous websites (“.onion” sites) that do not exist on the clear or surface web.
- With pre-attack intelligence on the reconnaissance threat actors undertake on the deep and dark web.
- In 2025, I used Haystak to find a historical .onion archive of a defunct hacking forum for a cybersecurity report.
- To get the full potential of SearXNG, especially for deep web content, use the Tor browser.
- From the main search page, you can link through to sites of specific institutions and even tribal governments, accessing all kinds of records from birth and death certificates to old legal information.
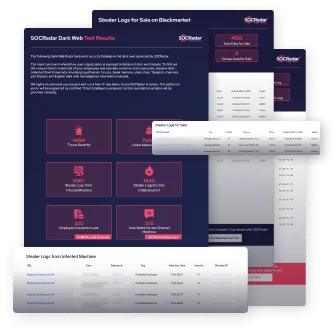
- Determine the risk of a cyberattack based on your level of dark web exposure.
Supercharge Your Security With Our Dark Web Monitoring Tool
According to my personal experience, Deep Search seems to provide pretty accurate and useful results, unlike others who spam users with spam links. Another noteworthy feature of Deep Search is that it provides a list of marketplaces, exchanges, and websites involved in scamming users. Onion Search is a search engine for the dark web that enables users to find and access Onion sites. The site is designed to be used with the Tor browser, which allows users to browse the internet anonymously. The Hidden Wiki is a dark web directory that can only be accessed using the Tor network. The Hidden Wiki is a valuable resource for those who wish to explore the dark web, as it provides a safe and easy way to access a variety of different sites.
The Evolution Of Deep Web Search Engines
Ahmia is a dark web search engine that provides a user-friendly way to explore dark web sites by indexing major onion URLs. It’s particularly useful for educational organizations, research teams, and cybersecurity analysts who need a reliable bridge to understand dark networks’ structure. These search engines specialize in indexing hidden services, making it easier for users to access content within the Tor network securely.

Online Best Dark Web Search Engines For Tor Browser
Although it’s not a search engine, it offers a categorized directory with indexed links to .onion web pages. While the Hidden Wiki isn’t entirely unrestricted, and uses filters to block many dangerous sites, it still lists some dubious sites that other search engines block. Keep reading to learn about the top dark web search engines and how to use them to more safely navigate the dark web.
What Is SecureDrop?
The Tor browser is open-source and is used to access the dark web, where data is encrypted and routed through multiple relays before reaching its destination. The surface web—which we use for searching day-to-day information—is only its tip. Many more layers of hidden content can be found below—in the deep and dark web.

Windows Shortcuts That Will Cut Your Work Time In Half
Another important feature is the service’s attractive dashboard, which simplifies complex threat intelligence management tasks. Ignite integrates with existing security systems, enabling teams to manage threats efficiently without disrupting workflows. Additionally, the platform supports customizable dashboards and automated workflows, reducing the manual effort required for threat analysis. Flashpoint Ignite also offers support and training resources, ensuring users maximize the platform’s capabilities. Some dark web engines try to filter out illegal content or prioritize verified, non-malicious services.
What Is The Blind Spot In Your Attack Surface?
Therefore, we try to solve this problem with some solutions close to the search engines we use in daily life. From malware and phishing attacks to misinformation and legal risks, exploring this hidden layer of the internet can be dangerous without proper precautions. Leveraging Brandefense’s solutions, including Dark Web Monitoring, Threat Intelligence, and Threat Detection, can help mitigate these risks effectively. This is especially beneficial for professionals in cybersecurity or research, who require quick access to specific types of information. Haystak is a dark web browser that offers better filtering features that help users refine their search results, enabling them to locate exactly what they need. Dark web search engines are an alternative to having high technical knowledge, something hackers, journalists, and security firms are used to.
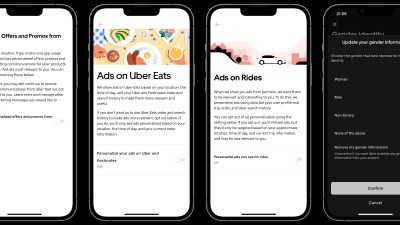
Tracking can happen through IP leaks, browser vulnerabilities, or malicious exit nodes. To reduce this risk, use the Tor Browser properly, keep your software updated, avoid sharing personal information, and pair it with a reliable VPN. Following best practices for online anonymity helps, but staying cautious is essential since no method is completely foolproof. Haystak boasts an impressive index of over 1.5 billion pages from more than 260,000 websites on the dark web. It offers both free and premium services, with the premium version providing additional features and more detailed results.
Risks And Precautions When Using OSINT Tools On The Dark Web
Osint sources include newspapers, magazines, news, conferences, photographs, videos, social media accounts, blogs, press conferences, and academic documents. With the spread of the Internet and the increase in the use of social media, there has been a significant increase in OSINT sources. The point to be considered is collecting information from resources that do not require contact with the target. The combined and automated use of OSINT techniques allows a threat actor to reveal its name, location, IP address, or image. OSINT, or Open Source Intelligence, can scan to Decipher and find connections between criminals and other actors around them. Specialists can also use it to monitor information such as possible attacks and internal threats, as well as to neutralize or disrupt plans in real time.
The 12 Best Deep Search Engines To Explore The Invisible Web
It’s not just a shadowy corner of the internet filled with illegal activities; it’s a realm where privacy is prioritized and unique resources are abundant. For the curious explorer, a dark web search engine is an indispensable tool. But what exactly is the dark web, and why does it need special search engines? Let’s dive deeper and explore the nuances of the dark web, the tools for navigating it, and the essential role of a VPN like Forest VPN in this journey. It allows users to suggest new .onion sites, but it does not indicate how these submissions are vetted, if at all, which can lead to low-quality, potentially harmful links appearing in search results. However, its open model and user-driven content curation allow cybersecurity researchers and experienced professionals to access a wider range of dark web sites.
The Express plan is best for SMBs, while the other is for mid-sized and large organizations. Moreover, you can integrate this solution into primary tools like SIEM and SOAR, making it one of the best dark web monitoring solutions. To mitigate these risks while exploring the dark web, it is crucial to use a reputable dark web browser like Octo coupled with proxies for an added layer of security. Keep your software always up-to-date, exercise extreme caution when clicking on links or downloading files, and avoid sharing personal information. Understanding the inherent dangers of the dark web and taking proactive safety measures are essential for a secure dark web experience.
Similar to using a regular web browser to access the surface web, visiting the darknet is legal. Regardless of the browser’s anonymity, it is still illegal to commit fraud or engage in any illegal activity on the dark web. According to a 2020 estimate conducted by Prey Project (a security service platform), 57% of the dark web is illegal. The dark web isn’t indexed by regular search engines and is known as a hotbed of criminal activity. NotEvil is a valuable tool for navigating the dark web while maintaining privacy. It indexes a variety of content, from privacy-focused services to news and forums, making it a useful resource for users seeking information beyond the surface web.