Whether you’re exploring it out of curiosity or for legitimate personal reasons, it’s essential to approach this hidden realm with the right knowledge, tools, and security measures. This high-security level makes the Tor browser fit for opening ‘onion’ links (dark web links), which use onion routing with several layers of encryption to protect your online traffic. The browser itself bounces web requests over three servers while encrypting the data before the request gets to the intended server. Most darknet market administrators are now tightening access controls.

Always remain vigilant about the risks involved with risky behavior, even when browsing through Tor. Downloading files from the Tor browser can compromise your anonymity. Malicious files might bypass Tor’s security, giving away your real IP address.

Tor relays are servers run by volunteers, designed to keep your activities private and untraceable. A VPN hides your internet activity, making it harder for your connection requests to be traced back to you. It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles. Please check your local laws to ensure your use of VPN complies with statutory requirements.
Minimize Or Rescale Your Tor Browsing Window
Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries. It is similar to an online store, except it’s not the type you’ll find with a quick Google search. For an extra sense of security, try a powerful identity theft protection service like LifeLock Standard that offers dark web monitoring.
User Reviews
The dark web has several convenient uses, which are not all basic. People who live under a government that deeply supervises or censors internet traffic eventually get attracted to the dark web. The other group of people is the one that requires the secrecy of the deep web to avoid pessimistic consequences – and to avoid trials. This group consists of a populace whose actions on the internet would rapidly lead to imprisonment or fines.
The same forgers advertise printing templates and hologram overlays, turning any high‑resolution printer into a fake‑ID mill.
The last thing you need to do is to start researching vendors and determine what marketplace is a possible vendor to buy the products from. Click on “Safest.” As you’ll see, JavaScript and a few other features will be automatically disabled on all sites. Be warned that this may cause some websites to not work properly.
The Future Of Anonymity And Privacy Tools
- Law enforcement regularly shuts down these markets, but new ones continuously emerge.
- Belarus requires VPN providers to register with the government, and unregistered use can trigger administrative fines.
- These markets operate on the dark web, which is a part of the internet that is not indexed by search engines and requires special software to access.
- Reports of hitmen for hire and crowdfunded assassinations on the dark web are believed to be hoaxes.
The Guardian newspaper has a SecureDrop facility on Tor – as does the CIA – which uses it for virtual walk-ins for anyone wanting to confidentially pass them information. This is where things might get just a bit confusing, as the Dark Web is nearly synonymous with illegal activity. Indeed, the vast majority of activity taking place there is illegal. In attempting to access the Dark Web, there’s an invisible line that a person acknowledges they’re crossing – or maybe they don’t. Either way, no one is accessing the Dark Web with a sense of optimism.
Get A Premium VPN
On the dark web, you’re expected to find illegal and prescription drugs (including Marijuana). Also, some toxic chemicals are peddled on the dark web that may cause severe damage to the targets. For this reason, users should be cautious when using their browsers.
How Does The Tor Browser Work?
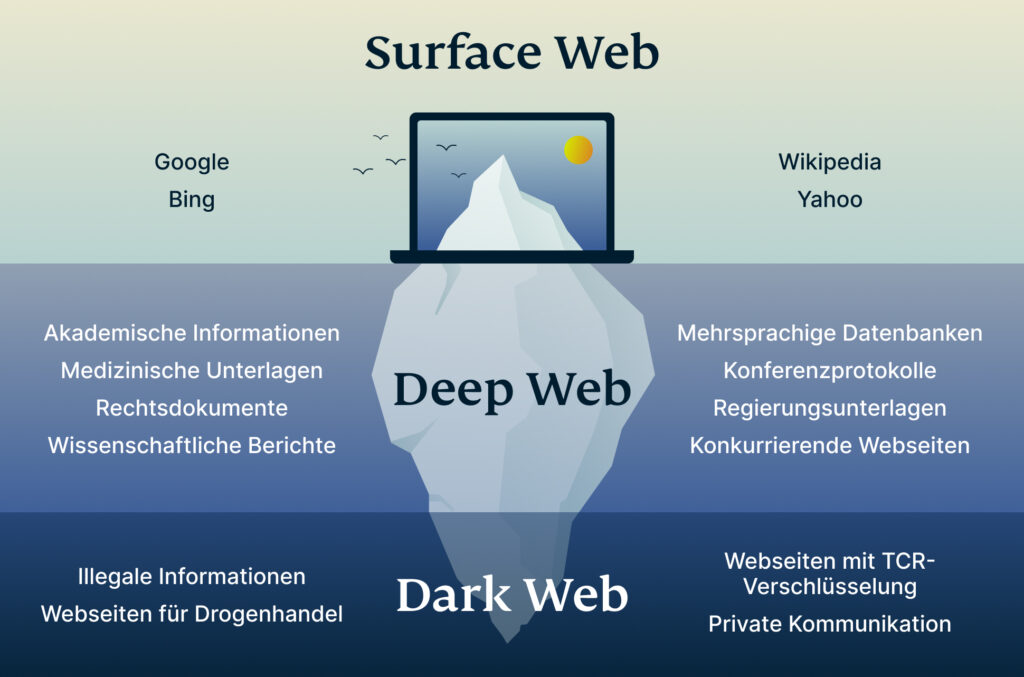
If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. The dark web, for the uninitiated among you, is a virtual neighborhood beyond the borders of the normal, everyday internet (which includes the website you’re looking at right now). It’s somewhere Google and Bing don’t index, and you need special tools to get to it. For added security, consider using a reliable VPN in conjunction with Tor. A VPN can mask your Tor usage from your Internet Service Provider (ISP), but be cautious — some VPN providers keep logs that could compromise your anonymity.
Cryptocurrency Transactions
The stolen data can be just anything from full names, credit card details, passwords to social media accounts, bank account information, and social security details, among others. Nevertheless, most of the items in the darknet markets are illegal or heavily regulated. In fact, according to a study that was done in 2020, over 57% of the websites found on the Tor network contained illegal content. We may just have heard of the Dark Web if you are a curious person to seek to explore the depths of the Internet. This secret portion of the Internet is inaccessible via standard search engines and requires specialized software, setups, and Dark Web credentials to reach.
- Even platforms like Netflix, which require paid access, are technically part of the Deep Web.
- Because of this it’s important to stay updated on which markets are active and which ones are no longer working.
- Also, it is worth noting that using Tor may draw attention from authorities if they suspect you are engaging in illegal activities or if your online behavior raises suspicion.
- This market is not open to the general public and is subject to a thorough vetting process to ensure its security.
- The VPN over Tor technique is also susceptible to an end-to-end timing attack, though it’s highly unlikely.
She yearns to know everything about the latest technology developments. Specifically, she’s crazy about the three C’s; computing, cybersecurity, and communication. However, Wright’s book isn’t well written and contains grammatical errors. If that’s not a turn-off for you, the book contains helpful information to boost your knowledge of the dark web. This isn’t just a matter of heading to “darkweb.com” and having a snoop — you’ll need specific software and a dedicated browser.
Also, since the Tor Browser is based on the Mozilla Firefox platform, it’s susceptible to the same attacks that other browsers are. DefCon, ProPublica, the CIA, various libraries, and open-source software providers also feature in this area of the internet. It will normally take a while to connect because Tor — unlike other browsers — will route your traffic through different nodes.
Drug Hub Market
The Tor network was created by the US military in the 1990s for anonymous communication between spies over the internet. That effort was never fully realized, but the US military published the code under a free license in 2004. Researchers from the Electronic Frontier Foundation and other groups continued its development and launched the Tor project in 2006 as a tool for journalists, activists, and whistleblowers. The big downside is that your ISP will know you are using Tor, which is cause for concern in some places and will put many people off using this method.



