
I also included instructions on how to access the dark web, and outlined how to stay safe when browsing dark web links (the dark web is also home to many scams and malicious sites). The marketplace was offline last week, when Dread and its sister services were under heavy DDoS and inaccessible. Prior to AlphaBay, Alexander Cazes had a reputable history on the darknet – specifically in the carding community. A senior member from the carding community Ranklez claimed he had evidence to suggest Cazes wasn’t alpha02. Ranklez and alpha02 had a history in the carding community as Ranklez sold alpha02 fullz for conducting identity theft. “This is the single most significant law enforcement disruption of the darknet to date,” U.S.
You can find featured listings on the homepage and browse the products of your choice. There’s also a search bar that you can use to search for any particular product or vendor. The White House market offers impressive features like a mandatory PGP requirement that enables 2FA for the user’s profile and adds a protective layer.
Best Free VPNs For The Dark Web In 2025: Secure & Fast

As a result, we want you to stay safe and anonymous by using a paid VPN service whenever you surf this dark web platform. Knowing this, we tested many dark websites, and only the safest and most reliable ones made it to our list of 29 best dark web sites you should know in 2025. Onion sites are slower than regular websites due to Tor’s privacy-focused design. Tor uses multi-layered encryption and routes data through multiple relays (entry, middle, and exit nodes), which increases latency to enhance anonymity. No, simply entering or browsing the Dark Web itself isn’t illegal in most countries.
STYX Market
Serving 15,000+ users and 1,200+ vendors, it holds an 8% share of darknet drug trading. Known for its robust escrow security and diverse offerings, Abacus is a top choice for 2025. In this article, you’ll find detailed overviews of the top ten Dark-Web marketplaces currently dominating the hidden internet landscape in 2025.
Cyber-Attacks And Scams
This market has also introduced AI-driven vendor verification systems, ensuring that only reputable sellers are allowed to operate. NebulaTrade’s emphasis on quality control has made it a preferred choice for buyers seeking consistent and high-quality products. When visiting the dark web, use a secure browser like Tor, do not reveal any of your personal information, and don’t open suspicious files or links to stay safe. As a result, your dark web use may draw unwanted scrutiny from your ISP or law enforcement. Using a VPN can help strengthen your privacy while visiting the dark web.
Exploring The Use Cases Of Darknets & Dark Markets
Like other marketplaces, ASAP Market also requires you to register for an account. The marketplace has several rules that every user is bound to follow. If any user is found not complying with the law, strict and immediate action will be taken against them. It uses PGP encryption to protect sensitive data and messages, and accepts payments via Monera and Bitcoins to keep you anonymous on this marketplace. Vice City Market is a new and cutting-edge dark web marketplace where you can find a range of products and vendors at an affordable price (compared to the damage they do to the victims).
Top Darknet Market Comparison Chart 2025
The Tor browser option for streaming comes with eleven channels with varying genres. But, honestly, if you are going on the dark just to enjoy free music, we recommend that you go for free torrent platforms on the surface web instead. If you wish to access the snapshots of these websites, just type in the domain name, and you will get the results depending on how many records exist on the website. It saves a select version of each page and preserves it even after upgrades have taken effect on the original site. However, not all books on this site are legally available, so they don’t have copyrights.
Topics And Products Sold

Using TAILS is yet another security measure that protects your online identity on the dark web. It is a specific Debian-based version of Linux software that leaves no traces of the user activity or the operating system on the computer. It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.

Search Engines
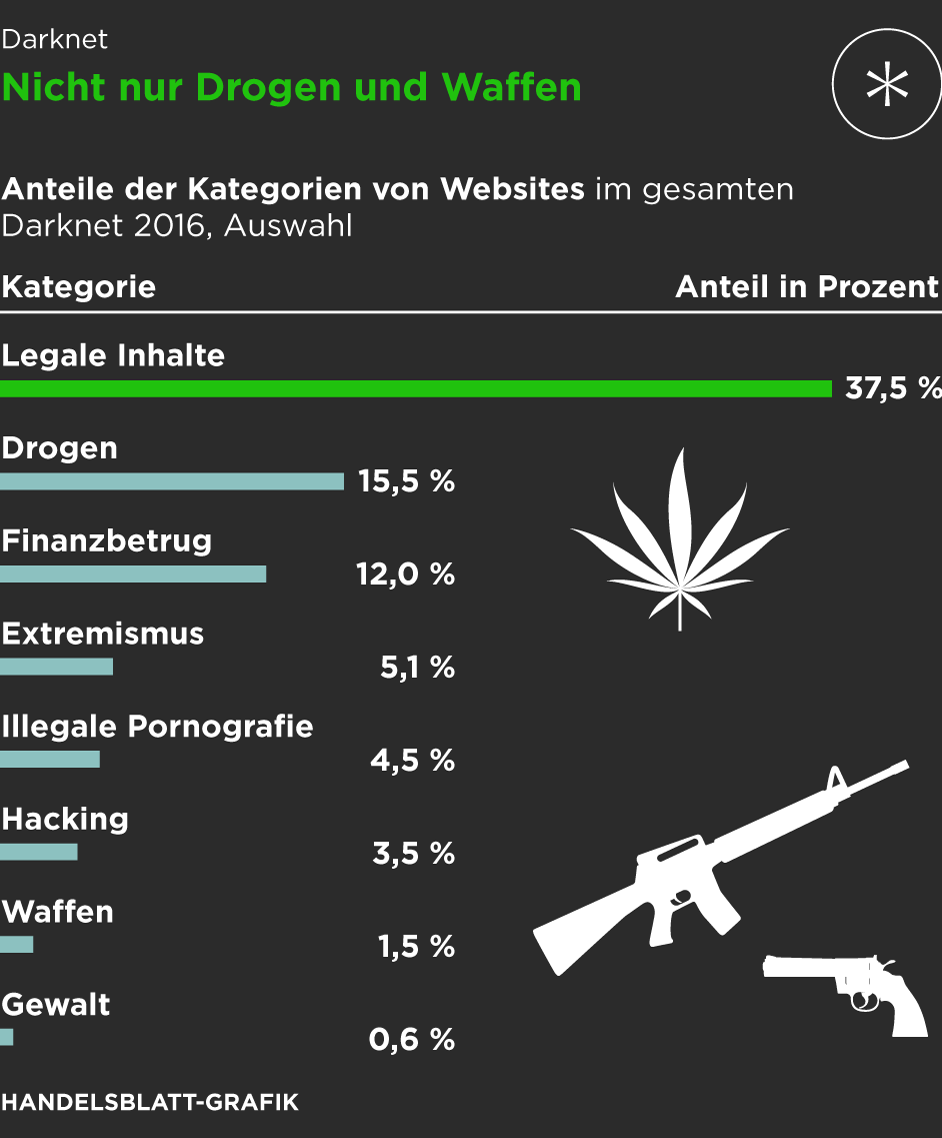
New darknet sites and markets continuously emerge to replace those that get shut down. The technology behind the darknet is actively maintained and continues to evolve. Personal and financial data are commonly sold on dark markets, facilitating identity theft and fraudulent activities.
The service remains free to use, and the secure design prevents access to third parties, eavesdroppers, and other malicious agents. To contribute a tip, join the community, which can be done anonymously through an approved onion link. The site is strongly resistant to hackers and encrypts your data in transit as well as the rest. This is a blog with cybersecurity tips created by the Electronic Frontier Foundation (EFF), a popular non-profit that specializes in digital privacy.
- Bitcoin’s blockchain is too leaky these days, and markets like Archetyp going Monero-only prove it.
- It has a wide range of products, including drugs, counterfeit items, and services.
- By learning to recognize these ploys and adopting defensive habits, you can significantly reduce the risk of becoming a victim.
- If you get a reliable vendor, you should procure the services to stay safe when accessing the dark web.
- This explains how the market of the dark web marketplace is affected.
A VPN also encrypts your connection, keeping your data safe from surveillance and unauthorized access. Torch is one of the oldest and most reliable search engines on the Dark Web, with a database containing one of the largest indexes of .onion sites. It’s primarily funded through ads and doesn’t filter search results. As a result, you may see adult content, gambling, or other offensive websites during your searches, so be careful about the links you click. For security and anonymity purposes the marketplace encourages all users to install a PGP key and to use two-factor authentication for accounts.
This is no different from the “.net” or “.com” of the regular Internet. Sheharyar is a passionate tech-writer who believes in the digital freedom and online privacy of all. He regularly tests and analyzes different VPNs to give accurate and up-to-date user-guides and comparisons.



