
They can then sell the account credentials to a buyer who can log in and drains the funds, or the vendor can transfer the requested amount of money from the victim’s account to the buyer’s account. Discover the pros and cons of using credit cards or card for purchases, including benefits and risks, to make informed financial decisions. Stolen credit card details can be categorized into different types, making it easier for cybercriminals to exploit them. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. As with our previous reports, we gather data by scanning Dark Web marketplaces, forums, and websites.
Cybersecurity Workforce Trends In 2025 – Skills Gap, Diversity And SOC Readiness
No wonder credit monitoring companies have added dark web winds up in this underground cyber-marketplace or prevent it from being sold. Like Litecoin and Monero arecurrently making waves in the market and this is due to payment systems (wire transfers, or credit card payments) provide. We investigated how the Dark Web market has changed since our previously reported Dark Web Price Credit card details, account balance up to 1,000, 150.

After it relaunched in June 2022, BidenCash initiated a promotional campaign that included sharing a dump of 8 million lines of compromised data for sale, which included thousands of stolen credit cards. Deep and dark web credit card sites include forums and marketplaces that host the trade and share of illicit content relating to credit cards. These stats highlight the scale of credit card fraud on dark web markets. 1 Next, we’ll look at how this sensitive data ends up for sale online. To do this, we first identified 30 darknet markets advertising stolen data products. It is common to hear news reports about large data breaches, but what happens once your personal data is stolen?
Blitz Malware: A Tale Of Game Cheats And Code Repositories
Discover everything about what a darknet market is, top marketplaces, security threats on them, and learn how to protect your data online. Launched in September 2022, Torzon Market operates on the Tor network and features over 11,600 illegal products, including drugs and hacking tools. It enhances buyer transparency by importing vendor feedback with PGP proof. Torzon offers a premium account option for additional benefits and is valued at approximately $15 million, accepting payments in Bitcoin (BTC) and Monero (XMR). These sites cater to cybercriminals seeking valuable data, such as credit card numbers, login credentials, and personal information.
Threat Brief: Escalation Of Cyber Risk Related To Iran (Updated June
N 2025, dark web websites frequently change domains and are often short-lived. Accessing them may require .onion links and the Tor browser, but caution is advised due to legality and cybersecurity risks. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last.
Why Is It Critical To Monitor Dark Web Marketplaces?

Guns, credit card information, specialty items (Ebola-tainted blood. If you know the right people and if you can get other criminals to vouch for you you can go online and buy huge bundles of stolen credit. Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information. These platforms serve as hubs for cybercriminals to buy and sell compromised payment card details. The sooner you become aware of compromised information, such as stolen credit card numbers on dark web, the faster you can take steps to mitigate damage. Rapid response can prevent unauthorized transactions, minimize financial losses, and protect your customers’ trust in your business. B1ack’s Stash’s emergence and rapid growth highlight the ongoing evolution of dark web marketplaces and the persistent threats they pose to global cybersecurity.

What Should I Do If My Card Is Stolen?
An individual who wants to buy a product in the darknet market needs to credit his/her darknet market account with Bitcoins to make purchases in the darknet market. The buyer purchases and moves Bitcoins to the darknet user account used by the buyer and makes the desired purchase. Once the buyer has initiated the purchase, the respective cost of the purchase in Bitcoins from the buyer’s account are held in the darknet market’s escrow until the order has been completed. Once the purchase order has been completed, the Bitcoins are released to the Seller (Vendor). The figure below shows a flowchart of the payment model being used in darknet markets.
The Evolution Of Carding And Its Present-day Form
The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. This explains how the market of the dark web marketplace is affected. As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. It became the blueprint for other dark web marketplaces that tried to take its place. These hackers don’t hide in the shadows as much as you might think. In fact, many openly advertise their services on darknet forums.
- Despite minor accessibility inconveniences, these strengths have solidified its position among the top dark-web marketplaces in 2025.
- The second category consists of data stores, which specialize in stolen information.
- The story of dark web marketplaces kicks off with Silk Road, launched in 2011.
- There are many types of malicious tools and services being sold in the darknet markets, some of which we have already shared in part 2 of our cybercrime underground series.
- Russian Market has consistently remained one of the most popular and valuable data stores on the dark web.
Why Are Darknet Markets Found On The Dark Web?
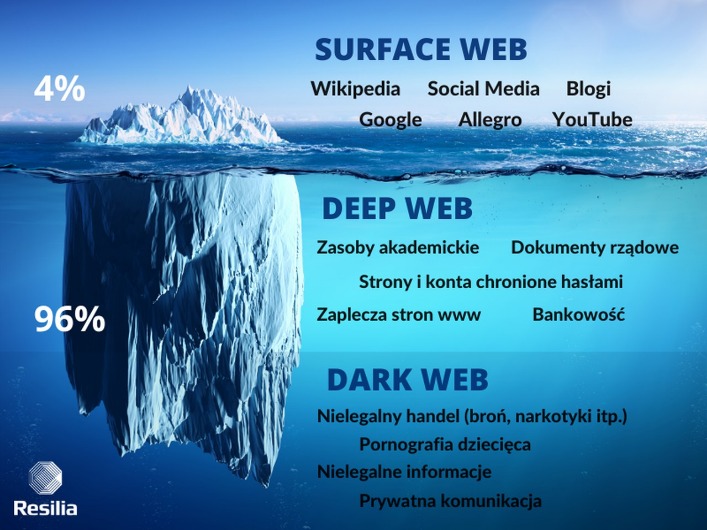
So, what even is this dark web, and why are these marketplaces present there? If you ever decide to explore the dark web, protecting your identity is crucial. Most people start by using the Tor Browser, which hides your IP address.

How Technology Is Evolving To Counter Card Fraud On The Dark Web
It is being sold only once and exclusively to one buyer until the vulnerability is public or an alternate exploit has been published. Empire Market, one of the biggest darknets market has reportedly exit scammed customers after operations have been shutdown for a couple of days, this week. Reports say that even though the DNM operators have stolen around grey market darknet 2,638 BTC, onchain funds stemming from the DNM have not moved yet. In March, the mostly Europe-based buyers made 14,289 pot purchases on the markets Cannazon, Versus, and Agartha, compared with just 11,036 in January, a 30 percent increase.
- Most darknet markets have a .onion TLD suffix which states that it is a hidden service and can only be reachable by the TOR network.
- This proven technology, seamlessly working in the background, analyses transaction data and authenticates users in real-time, ensuring only legitimate transactions proceed.
- Carding shops are a type of dark web marketplace that hosts the trade of credit cards and other stolen financial information.
- The number of card packages offered on the site has consistently increased, and today it also has an active Telegram channel from which it operates and sells stolen credit card details and announces new dumps.
- Two-factor authentication adds a second layer of defense by requiring special codes or biometrics before you — or anyone — can get into your accounts.
- As long as people want to buy and sell illegal stuff online, be it stolen data, narcotics, drugs, or malware, these markets will keep resurfacing, no matter how many times authorities take them down.
While these marketplaces continue to serve legitimate purposes, such as enabling secure communication and privacy protection, they also remain hotspots for illicit activities and cybercrime. Overall, dark-web marketplaces inherently involve substantial risk, and users must thoroughly understand these threats. Anyone considering engaging with these platforms must carefully evaluate potential consequences, exercise stringent security practices, and remain vigilant to minimize exposure to these significant hazards.

No relationship is created with you, nor any duty of care assumed to you, when you use this blog. The blog is not a substitute for obtaining any legal, financial or any other form of professional advice from a suitably qualified and licensed advisor. The information on this blog may be changed without notice and is not guaranteed to be complete, accurate, correct or up-to-date.



