
Law enforcement and enterprises must leverage automation (e.g., Tor traffic detection, OSINT scraping) to stay ahead. Future darknet markets will likely adopt AI-driven obfuscation, necessitating AI-powered defense mechanisms. For the interpretation of a link as familiarity and shared interest, one can interpret a smaller distance as it being more likely for a user’s posts to be visible to other users.
Detecting Vendors In The User Base
Those additional security checks may include additional CAPTCHAs (i.e. making the session expire) and killing the current Tor circuit (i.e. changing the Tor identity needed). In practice, some markets have very restrictive thresholds, making it very challenging to obtain data for the entire market. For example, in Bohemia, our crawler operates at an average of ten requests per minute without the need for manual intervention for a long time. The trends observed in dark web markets are very dynamic and ever-changing. However, there is currently no literature that comprehensively describes the security mechanisms implemented by dark web markets.
Popular Dark Web Marketplaces

The development community that supports Monero is broken into various workgroups with roles that include infrastructure, community, development, regulatory compliance and more. Ehrenhofer’s Monero Space workgroup, for example, provides a number of services to the coin’s community. “By just providing a very basic level of privacy protection to everyone, it means that you can, in practice, treat Monero as fungible, which helps with commerce,” he said. “So when you see people actually accepting cryptocurrency payments, Monero is really high up there.” “Monero takes privacy seriously. Monero needs to be able to protect users in a court of law and, in extreme cases, from the death penalty,” the site reads. Perhaps because of this, some major cryptocurrency exchanges like Coinbase do not offer Monero transactions.
The Increasing Risk Of Data Breaches
Special characters are mostly not supported, but underscore and dash are accepted in two markets. Generally speaking, some CAPTCHAs seem to be difficult to solve, and some even have strict time limits (i.e. the users need to solve them correctly within a limited time). However, if we bring in the latest knowledge on CAPTCHA generation and breaking from the security community, these CAPTCHAs are all trivial to break. It seems that CAPTCHA designers for dark web markets, fortunately (and unsurprisingly) do not follow recent academic literature in the topic, and it absolutely shows in their designs. Darknet marketplaces remain central to illicit trade in 2025, with evolving business models, payment systems, and law enforcement responses.
Exodus Marketplace
In this darkest corner of the internet, that gun becomes an illegal weapon. Besides, not everyone wants to purchase an illegal item – some want items anonymously. Discover everything about what is a darknet market, how it works, security threats related to it, and learn how to protect your data online. Darknet marketplaces emerged around 2011, with Silk Road setting the standard for how these platforms operate. Built on Tor, these sites mask IP addresses by routing traffic through encrypted relays, ensuring anonymity for both buyers and sellers.
Password And Login Protection
This includes regularly updating software, using strong passwords, and enabling two-factor authentication. We’ll also discuss strategies for protecting yourself and your organization from the threats posed by darknet markets. Torzon Market has established itself as a significant player in the darknet ecosystem, offering a secure, user-centric platform for anonymous trading. Its commitment to privacy, diverse product offerings, and robust security measures make it a preferred choice for users seeking discreet transactions within the darknet. These takedowns actively disrupt the immediate activities of these marketplaces and also cause a greater ripple effect, creating mistrust among other dark web users and making it harder for new markets to gain traction.
BidenCash is another latest marketplace that started in 2022, and is now home to sensitive financial data transactions. This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself.
Best Dark Web Sites In 2025 (Unseen Onion, Tor Links)
- Integrated protection features within the kerberos official site system actively prevent unauthorized access attempts.
- Governments around the world have recognized the growing threat of darknet markets and have been actively working together to develop global regulatory frameworks.
- In the interview, the admin claims that a certain substance turned his life around, and that he now believes drugs should be legalized, which is why he made the site.
- After purchasing an item, the funds will still be held in the market wallet.
- However, they also include the more successful vendors that are responsible for the majority of the trade conducted on the cryptomarket.
“And those records helped law enforcement uncover the true identities of many of the users,” the official said. U.S. officials said Genesis Market was not only a seller of stolen account access credentials but was also “one of the most prolific” initial access brokers operating on the darknet. However, Europol confirmed for the first time today that Monopoly Market had been seized by German authorities in 2021 and used to collect evidence on the vendors and customers who bought and sold drugs on the site.

Every potential participant’s credentials must be vigorously vetted before they can join. That way, they aim to create secure forums and limit outsiders like law enforcement. Likewise, law enforcement agencies each day continue to fine-tune their strategies to get past these networks.
Avalanche Sees 66% Growth In Transactions With Government Adoption
Bitcoin was initially used to process payments, offering pseudonymity rather than full anonymity. Users must look for platforms employing robust encryption protocols, secure escrow services, and advanced anti-phishing measures. Additional layers, such as two-factor authentication (2FA), encrypted PGP messaging, and built-in wallet security, significantly enhance protection against theft and hacking. Another notable trend is the rise of encrypted peer-to-peer (P2P) messaging systems integrated directly within marketplaces, providing secure communication channels between buyers and sellers.
The more informed and vigilant we all are, the better we can tackle the challenges posed by the dark web. A well-informed community is a strong line of defense against these underground markets and their illegal activities. Undercover operations are also vital for these operations, with agents posing as buyers or sellers to infiltrate these markets.
Similar Content Being Viewed By Others
As law enforcement continues to innovate and adapt, their ongoing efforts and international collaboration remain crucial in the fight against dark web crime. There are a lot of misconceptions about the dark web online and in popular media. When most people refer to the dark web, they are thinking about dark web/darknet marketplaces (DNMs). The re-emergence of Black Ops underscores the need for adaptive cybersecurity strategies.
- All communications are encrypted using PGP keys, and payments are processed through anonymous cryptocurrency wallets.
- As such, betweenness centrality is the network measure most likely to be of use to law enforcement for detecting vendors in the user base.
- Recognizing that criminal operations extend beyond national borders, agencies collaborate with counterparts from different countries to share information and resources.
- Markets like AlphaBay and Hansa adopted stronger encryption and expanded offerings to include hacking tools and stolen data.
- In other words, it measures how important a node is with respect to connecting various communities in the network.
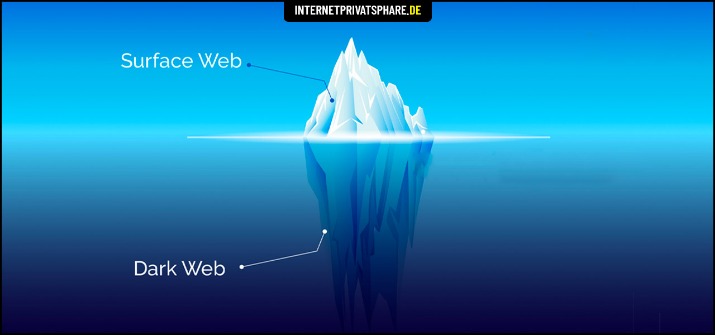
Who doesn’t like privacy, especially when dealing with the buying and selling of illegal products and services? Therefore, given the nature of anonymity and privacy of the dark web, several stores keep on emerging in the dark despite a continuous crackdown on several others. The darknet is basically an overlay network that exists within the internet and can only be accessed with specific configurations, software, and usually uses certain customized communication protocols. The internet is a wide landscape that comprises the surface part – the internet that we all know and the hidden portion. The hidden part of the internet is the larger portion that features over 95% of the entire internet.



