The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet.
- Some services are genuine; you can get what you want at an agreed fee.
- It is similar to an online store, except it’s not the type you’ll find with a quick Google search.
- Unlike regular e-commerce sites, markets on the dark web often deal with illegal or highly restricted goods and services, such as fake documents, hard drugs, and hacking services.
- But somewhere between production and purchasing, things can get dirty.
- Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.
- Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
It also runs on the Tor network, which helps keep things anonymous. A 2014 study found that the most common type of content found on Tor, the most popular darknet, was child sexual abuse material. Cybersecurity companies and researchers monitoring darknet markets face legal and ethical restrictions.
Espionage And National Security Threats
This means that the servers providing these services are only accessible via Tor and do not have a public IP address or domain name. Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging. Background research tasks included learning from past drug lords, researching legal matters, studying law enforcement agency tactics and obtaining legal representation.
However, this feature is only available on iOS, Android, and Windows. The most interesting thing about NordVPN is its built-in Onion over VPN feature. It encrypts your traffic at the entry node and changes your IP address. This means you will get a VPN’s security and enjoy the anonymity of the Tor network simultaneously. Today, many organizations exist that are created only to handle these reports anonymously and effectively.
Q: Should I Use A VPN?
The VPN will protect your traffic when you connect with military-grade AES 256-bit encryption. This is high-level protection; no one can intercept your data or activities. A virtual private network (VPN) is a good way to mask Tor activities. It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. The Tor browser allows you to browse the internet anonymously and visit inaccessible sites. It will encrypt your traffic and data so no one can intercept it.
Archetyp Market
In addition, it ensures that no record of communication is stored. Freshtools is a unique marketplace in that it does not only provide the stolen data, but it allows criminals to purchase MaaS which can cause further damage to the victims. It is one of the most active and up to date markets and always provides new and updated malware and data.

Key Cyber Threats Facing The Financial Sector In 2025
These tools enable a rapidly growing cohort of organizations around the world to safely embrace cryptocurrency-related transactions, products, and partnerships. You can use dark web monitoring tools, such as NordVPN’s Dark Web Monitor, to check if your data has been leaked. These tools scan dark web forums and marketplaces for any signs of your compromised credentials. There is no need to visit darknet marketplaces yourself to know whether your data was leaked. Some vendors offer services to help people “clean” illegally obtained funds using cryptocurrency and fake transactions.
Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom. The creators assert that because their technique is so strong, even malware with root access could not determine the machine’s IP address. To prevent detection, the program runs user data via a tiered stream before allowing access to the dark web. I2P, or the Invisible Internet Project, allows you to access the ordinary and dark web. Specifically, the I2P darknet is accessible, while the Tor network is accessible through the Orchid Outproxy Tor plugin.
Key Features
As much as authorities work hard to shut down various sites, it shows what the dark web is capable of doing if left unchecked. The dark web is famous when it comes to hosting as well as spreading explicit and illegal content. It is home to all sorts of disturbing content, given that the markets share content related to non-consensual recordings and child exploitation. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust.
The Beginning: ARPANET And The Birth Of Anonymity (1960s-1990s)
You face significant risks when using dark markets, including scams where vendors take payment without delivering goods. There’s high exposure to malware and cybersecurity threats that can steal your personal information. Law enforcement agencies actively monitor these markets and can track users despite anonymity measures. You risk legal consequences if caught participating in illegal transactions. Financial fraud is common, and you have no recourse if transactions go wrong since these markets operate outside legal frameworks.

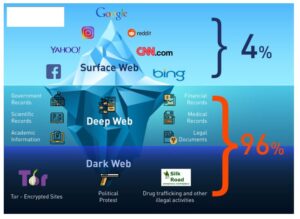
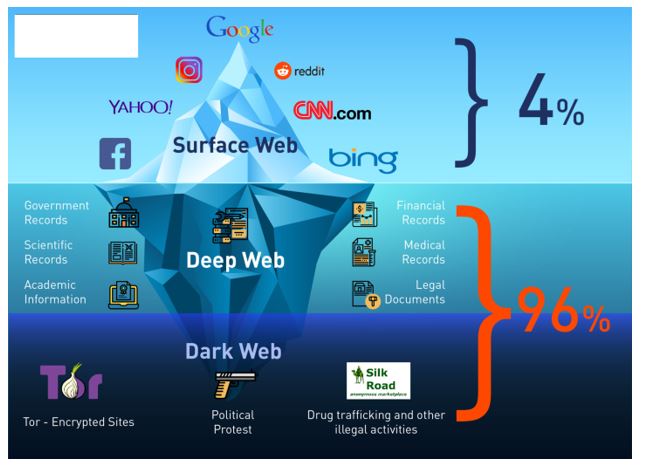
With rising online privacy concerns in the current digital age, the Tor network’s anonymity is becoming essential. It is a good way to prevent third parties from tracking online activities. People in countries with heavy internet censorship must get a VPN or Tor browser to access the surface web. Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
- In this system, cryptocurrency is held by a trusted third party until the buyer receives the product or service as described.
- Discover a reliable platform for a variety of products, including exclusive offers and top-rated vendors.
- While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing.
- The dark web is not a place that you can venture into without protection and caution; a slight slip-up can lead to major consequences.
Whether you want some pharmaceutical products (drugs) or digital items, you will probably find the products here, and that too at affordable prices. Vice City listens to the problems faced by its customers and vendors and solves them so that they can keep using the platform with ease. To access the marketplace, dark web users must register first and pass the CAPTCHA test to prove they are human. The site allows users to find and buy a vast variety of products and services. It’s known for its strong security features (like a trusted escrow system, PGP two-factor authentication) and anonymity.

Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they have better security than the older ones. Darknets are not limited to criminal activities; nation-state actors use these hidden platforms for espionage, disseminating propaganda, and recruiting agents. The significance lies in the potential compromise of national security.