In fact, more of them keep popping up and gaining traction. Stopping their growth takes serious effort from US agencies like the FBI, often working hand-in-hand with international law enforcement. From there, these products are then passed on to distributors, which are the dark web marketplaces in this context. On these marketplaces, they’re listed, sold, and promoted just like items on any e-commerce site. If you think the Dark web marketplaces are just online shops, you’re wrong — these sites are the actual weapon stores for criminals.
How To Access The Dark Web Safely
Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started. TOR Browser is a free, modified version of the Firefox web browser configured to connect to the TOR network. You may also use it to access the regular internet more anonymously. Standard search engines index these websites and are accessible without special configuration.

Eventually, the system collapses, and most people lose their entire investment. So, if a “business opportunity” sounds too perfect, it probably is. Once many users begin to rely on the site and store funds in escrow, the operators disappear, taking all the money with them and leaving their customers and clients with nothing. Imagine trusting a site where you’ve been buying or selling for months, and everything seems legit. Some marketplace operators first build trust by running a legitimate platform.

OnionWallet
Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever. First things first, always use strong and different passwords for each account you open. Too-good-to-be-true investment offers are another classic scam on the dark web. Ponzi schemes promise high returns with little to no risk. Early participants may see some profit, but that money usually comes from new victims, not actual earnings.
Exploitation Of Anonymity For Harm
Dark Matter also runs an in-platform “Academy” with tutorials on PGP encryption, Monero use, and multisig transactions, catering to both newcomers and experienced darknet users. It features an experience-level system where users earn points for successful transactions, unlocking perks like personalized onion links. The market’s combination of privacy-first design, educational tools, and vendor transparency has earned it a solid reputation on darknet forums as a secure and stable option.
What To Look For In A Trusted Top Darknet Marketplaces
- Then, you can set up 2FA (two-factor authentication) for that extra touch of security in case someone somehow figures out your password.
- Fake cash flows too—I’ve heard of crisp euros passing at corner stores.
- In the categories for databases, stealer logs and combolists, there are always entries that point to leaked customer data, access data to Swiss online services or compromised business data.
- We’re not amateurs—we’re seasoned pros who guarantee results every time.
- Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria.
- These include drugs such as stimulants, cannabis and hashish, opioids, psychedelics and ecstasy, as well as fraud and financial data, including bank accounts, credit card details and other sensitive information.
While you could find all sorts of products on Silk Road, drug sales quickly became prevalent because of the profits it raked in. In fact, by 2013, a Guardian article revealed that about 70% of listings were drug-related. Remember, staying informed is your best defense against misinformation. When you know what to expect, you’re less likely to fall for a trick and should be able to keep your identity safe. Drug dealers can sell to customers across the world, not just locally. This expanded reach, combined with anonymity, only makes it easier for them to grow their operations without getting caught immediately.

Not all stolen identities are equal; some are worth more, and some people get targeted more often. Once sold, identities are used to commit fraud or bypass KYC checks. Once attackers get credentials, they test them across multiple platforms to see what else they can access. Additionally, communities facing rampant document fraud often see declining public trust in institutions, businesses, and even interpersonal relationships. When citizens perceive that fraud is widespread or tolerated, social cohesion weakens, damaging overall community resilience and stability. In educational institutions, routine use of fake IDs among students can foster environments of leniency toward rule-breaking, indirectly promoting a culture where dishonesty becomes normalized.
Impact On Businesses And Cybersecurity
For sellers, it’s profit maximisation without the hassle of licences, safety compliance, or traditional logistics. Saheed Aremu passionately advocates for digital privacy and cybersecurity in the modern digital age. As one of PrivacySavvy’s resident VPN experts, he guides readers on protecting their online information and anonymity. Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria. Since then, he has dedicated his career to writing extensively about crucial infosec, data privacy, and cybersecurity topics. When he’s not empowering PrivacySavvy’s readers to take control of their online security, Saheed enjoys distance running, playing chess, and exploring the latest open-source software advancements.
Did The Silk Road Marketplace Go Under?
These markets are a hot spot for selling stolen personal data. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information. The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses. Wondering if there’s an OG darknet market for financial crimes?
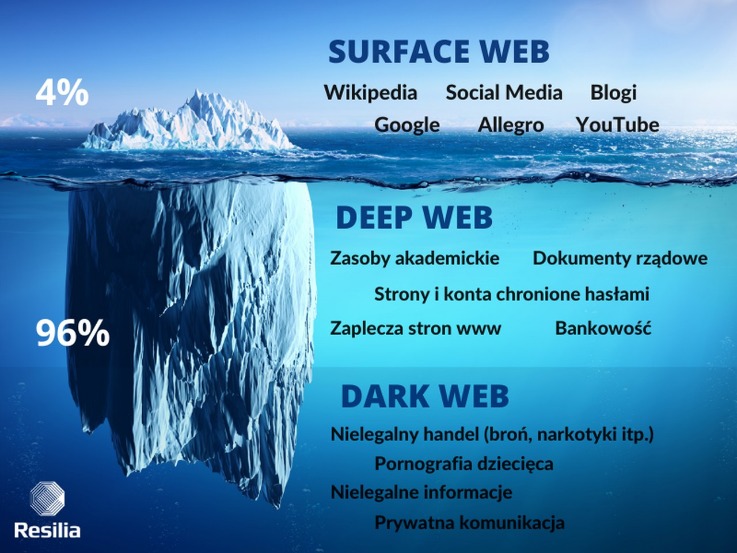
So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access. Pixel Privacy believes in digital privacy and does not believe in using it for heinous and/or illegal activities, and so the focus of this article will be on legal activities. It might sound weird that Google doesn’t index these pages, but it does carry some logical sense. Google’s purpose is to show the most relevant information to all of its users quickly and easily.
- A .onion site consists of 16 alphanumeric characters followed by a .onion TLD.
- From scannable barcodes that work flawlessly in any system to UV ink that lights up under blacklight, we replicate every modern security measure used in official IDs.
- DeepMarket is another one of these dark web sites that sell everything your local vendor won’t or can’t sell to you.
- On one hand, it offers privacy for whistleblowers, journalists, and citizens in oppressive countries.
- Image of counterfeit ID card and underground economy tools Artificially generated image.
The market facilitates trades in stolen credit card data, hacked bank accounts, and services to facilitate the laundering of cryptocurrency. Here is another financial marketplace operated by a group of highly skilled hackers (electronic and computer expert). In 2009, they launched website on darknet to sell credit cards, bank accounts, PayPal transfer, and western union.
Conclusion Are Top Darknet Marketplaces Still Relevant In 2025?
Here’s what your information is worth and how to protect it. It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack. I do not condone the use of DNMs to purchase or sell drugs and other illegal materials online. DNMs are inherently dangerous places and its users risk losing their money, their freedom, and their lives.Are you suffering from drug addiction?
DeepHole – 10x Your BitCoin In 24 Hours
Simply download the file, install the software, and you’re ready to use its web-based interface. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. In opennet mode, the network will automatically assign you to other users on Freenet’s network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN. Rule No.41 allows a federal judge to issue a search and seize warrant for any person who is using anonymity software like Tor.
Unlike many other dark web markets, Cypher does not require buyers to deposit cryptocurrency upfront, which reduces the risk of exit scams. Apart from the dark web markets that are operating online today, some raided platforms influenced many markets. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users. Various cryptocurrencies such as Bitcoin and Monero can be used to make purchases. The Abacus Market links to the new dark web marketplace sections and took over much of the vacuum left by the AlphaBay takedown. Security researchers have been monitoring forums within the cybercriminal underworld to investigate the leading markets operating in 2024.



