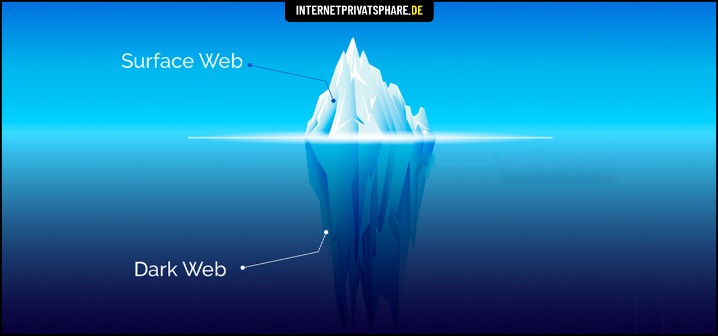
Policing involves targeting specific activities of the private web deemed illegal or subject to internet censorship. Your online activity and communications remain private and secret on the dark web. Because of this, some people use it to get around government restrictions, while others use it for illegal activities like smuggling drugs and weapons. Whereas the deep web is the part of the web not searchable by traditional search engines and requires special tools to access it. Also, you must log in or have a specific IP address or URL to access the deep web content.
Market Value And Popularity

Meanwhile, Facebook also offers dark web access to their social network. However, there are several “.onion” search engines like “onion.city”, “onion.to”, and “notevil” that you can use to find suitable marketplaces. NordVPN offers a 30-day, no-risk trial subscription when you sign up on this page. This provides a full month’s access to all of the features of the #1 VPN for the Dark Web. This is an excellent way for Dark Web users to provide additional privacy protection when accessing the Dark Web.
Measures Against The Trade In Illegal Data

For best security, you should encrypt yourself to be 100% sure that your message cannot be read by anyone else. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people.
The exit node decrypts your traffic and thus can steal your personal information or inject malicious code. Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either. That information is hidden simply because most users won’t find it relevant. Much of it is tucked away in databases that Google is either uninterested in or barred from crawling. Again, we can’t emphasize enough that security and anonymity are paramount to those on dark websites.
- But if we focus solely on the Dark Web, stats show its history dates back to 2000, when Ian Clarke released Freenet, his thesis project.
- The increased use of DeFi comes amid tight regulations on centralized exchanges.
- This encryption makes attribution and tracking more difficult for authorities and cybersecurity professionals.
- Experience Flare for yourself and see why Flare is used by organization’s including federal law enforcement, Fortune 50, financial institutions, and software startups.
What Is A Darknet Market?
While some studies have claimed that illegal Bitcoin activity is as high as 44%. You don’t need special tools or a special browser like you need to access the dark web (more about that later). Anyone can access the deep web by using specialized search engines, dedicated web directories, and other sources that can help you find the data or information. The Deep Web includes all content not indexed by search engines.This isn’t necessarily illegal—it’s just private or restricted.
Phishing Attacks

Obviously not all Tor users, but you never know whether someone might be looking into you. It’s important to arm yourself with a good VPN (Virtual Private Network) when you want to enter the dark web to protect your privacy and anonymity. The dark web is a decentralized web, which means that the data is stored on many different servers around the world. Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution. Those who access the dark web do so via the Tor (The Onion Router) browser.
How To Access The Dark Web: Step-by-Step Tutorial (and A Few Words Of Caution)
Many users find themselves cheated by false listings or fake vendors, losing their assets without recourse. Transactions on these platforms use an escrow system, where funds are held by the marketplace until the buyer confirms receipt of the goods. This layer of trust, though among criminals, helps ensure a safer exchange and mitigates risks of fraud. To maintain the secrecy that defines dark web markets, traditional payment methods are rarely used. Cryptocurrency has become the preferred means of exchange, with Bitcoin originally taking center stage.
The layers of encryption hide your data and activity from snooping eyes. Cyber threat intelligence (CTI) helps organizations predict, understand, and defend against cyber threats, enabling proactive protection and reducing the impact of attacks. Established in 2019, Russian Market is a well-known and highly regarded data store on the dark web, specializing in the sale of PII and various forms of stolen data.
- In fact, the Guardian referred to darknet markets as “the eBay of drug dealing,” and rightly so, illegal drugs are found in almost all the shops on the dark web.
- Especially for these people, the dark web is the perfect platform to communicate and publish information without having to worry about imprisonment or any other form of retribution.
- Many people go to the dark web to buy things they can’t find elsewhere, but what if what you’re buying is also trying to harm you?
- The integration of cryptocurrencies like Bitcoin and Monero remains a cornerstone of these platforms.
- For instance, after the closure of Genesis Market, its website came back after a few weeks.
The integration of cryptocurrencies like Bitcoin and Monero continues to provide unparalleled anonymity, making these markets a preferred choice for buyers and sellers alike. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025. Dark Web marketplaces are much like ecommerce websites on the Surface Web, but with one major difference — they mainly sell illicit and/or illegally obtained goods. These include stolen login credentials, credit card details, medical records, and cryptocurrencies.
Which Is The Best Laptop For Cyber Security Course?

It’s picking up steam fast, and I’d keep an eye on it if you like a community feel. Monero’s my go-to for dark web payments because it’s darn near impossible to trace. With tricks like ring signatures and stealth addresses, it keeps your transactions off the radar—unlike Bitcoin, which can leave a trail if you’re not careful. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details. Therefore, for security reasons, disable JavaScript on the Tor browser and enjoy an anonymous browsing experience on the dark net.
Yes, Onion.live and Haystak provide real-time updates and search functionalities for .onion sites. DeepPaste is a .onion-based paste site where users anonymously share encrypted text, often containing code, leaks, or confidential messages. Haystak is an advanced search engine for the dark web that offers a vast database of indexed .onion pages, helpful for professional intelligence collection. Onion.live is a platform that tracks the status of dark web sites and provides trust ratings to help users verify site legitimacy.
A handful of dark web search engines that do index .onion sites include NotEvil, Ahmia, Candle, and Torch. Western drug flows in particular come from US-domiciled exchanges and trace flows from those to darknet markets. The entity “DNM Aggregator” that appears within each category refers to a service we’ve identified as being in control of multiple, disparate darknet markets.
The Moneyzine.com stats team will then look at the usage data for Tor, the go-to browser for accessing the Dark Web. Finally, we’ll focus on the notorious Dark Web marketplaces, explore their history, and review the latest prices of various illicit items. However, your online activity is encrypted and hidden from view thanks to Tor’s onion routing. This means your ISP can’t see that you’re accessing the dark web (or indeed, the specific sites you’re accessing).
Legally, they are limited to observing publicly accessible areas using tools like the Tor browser, without engaging in unauthorized access or illegal transactions. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals. Classic darknet markets sell diverse illegal goods; data stores focus on leaked or stolen data like credentials, databases, and ID records.