The dark web might not interest you, but its denizens might have already cast their eyes on you, so approaching all of your business processes from a security-by-design perspective is essential. The dark web hosts a variety of illegal activities, many of which fuel cybercrime and real-world harm. For example, after the closure of the AlphaBay marketplace, other marketplaces, namely Hansa and Dream Market, experienced an abnormal spike in activity. In the first arc of the anime series Lupin the 3rd Part V, Lupin III steals digital currency from the “Marco Polo” darknet market. The months and years after Silk Road’s closure were marked by a greatly increased number of shorter-lived markets as well as semi-regular law enforcement takedowns, hacks, scams and voluntary closures.
Dark Web Markets: Unveiling The Hidden Underworld
Remember that illegal activities can still incriminate you, whether you are using a Tor browser. For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography. For example, it maintains your privacy and enables you to access untraceable content and services.
How To Protect Your Identity While Browsing The Dark Web
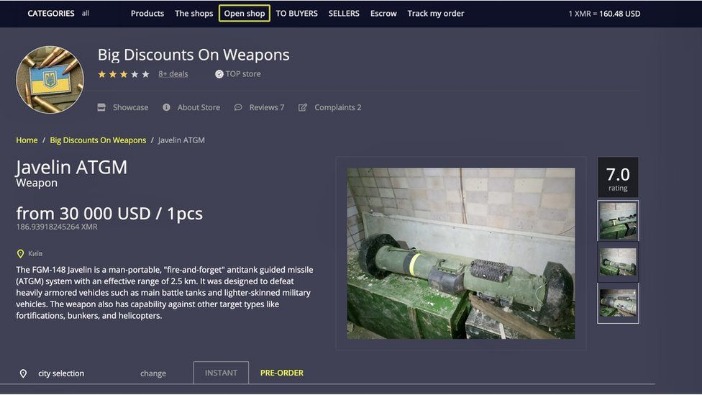
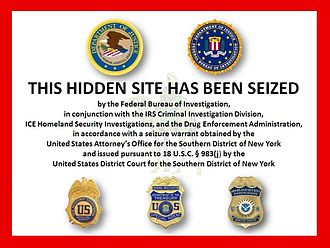
Its blend of simplicity, speed, and secure transactions makes it a reliable choice in the evolving darknet space. Transactions on these platforms use an escrow system, where funds are held by the marketplace until the buyer confirms receipt of the goods. This layer of trust, though among criminals, helps ensure a safer exchange and mitigates risks of fraud. Despite the attempts to secure the Silk Road’s activities, the platform caught the attention of law enforcement. In 2013, the FBI successfully traced Ulbricht and seized the Silk Road.
Similar Sites
- To reduce the presence of noise in the S2S network, we consider only stable U2U pairs, i.e., pairs that have at least three transactions throughout the whole period of observation13.
- Nemesis Market is a relatively new wallet-less shop on dark web where you don’t need to deposit any amount in your wallet before buying products from here.
- The evolution of the ecosystem of all buyers and sellers obtained from the considered markets and the U2U network is shown in Fig.
- Established in 2022, WizardShop is one of the biggest data stores on the dark web, focusing mainly on carding and financial data.
- Deep within the hidden recesses of the dark web, a marketplace called Tor2door has emerged as one of the most intriguing and concerning platforms for security professionals.
As explored in this article, the top dark web black markets demonstrate the growing sophistication and scale of these underground networks. For businesses and individuals alike, understanding these threats is the first step in securing their digital assets. However, combating dark web risks requires more than just awareness—it demands proactive and comprehensive protection. With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation. Our platform ensures that your brand stays one step ahead of cybercriminals, giving you peace of mind in an increasingly complex digital landscape. Explore how Brandefense can empower your brand to thrive securely, even in the shadow of the dark web.
Top Dark Web Marketplaces Of 2025: A Deeper Dive Into Illicit Trade Markets
- Shortly after Xennt arrived in the Mosel Valley, his activities attracted the interest of a prosecutor named Jörg Angerer, who worked in the nearby city of Koblenz.
- Unlike traditional e-commerce websites, these marketplaces rely on encrypted networks like Tor (The Onion Router) and cryptocurrencies such as Bitcoin to conceal user identities and transactions.
- You should never use your personal information on the dark web anywhere else in your life.
- Archetyp is a market that sells only drugs, and is still active today.
It may take anywhere from 15 seconds to several minutes for a page to load, depending on network and site demand. Many of these markets operate internationally, and some have certain specialties. To avoid immediate shutdown, the servers hosting DNMs must be in countries with lax legal regulations. This means the server admins must pay significantly higher hosting fees than they would on the clearnet, for less reliable service. The clearnet is the regular internet you’re used to using, where network traffic origins are fairly easy to pinpoint. It will route your traffic through multiple servers instead of one, making tracking your data and activities even harder.
Can WiFi Owners See Your Internet History?
For example, non-compliance can result in fines of up to 4% of an organization’s global annual revenue. After all, criminals are getting more creative and professional by the day, running their operations like businesses with customer service and even reviews. The growing shift toward more sophisticated and user-friendly criminal organizations is quickly becoming a real headache for cybersecurity firms. Our goal is to give cybersecurity professionals the scoop on the latest threats that have emerged and the best ways to fight back against these underground markets. By the end of this read, you’ll be armed with the knowledge you need to stay ahead of the game in the battle against dark web crime. Even passive activity on these sites can contribute to criminal networks.
If the above average Joe’s explanation isn’t enough for you, below are some legitimate reasons to use the Dark Web in a bit more detail. It’s important to note that although the dark web has many valuable services, it is also a hangout for cybercriminals. Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed.
The Role Of Forest VPN

Hence, you never know when a popular .onion site is going to vanish, or even die. Though it’s still helpful, a static list isn’t enough (we try to keep our own, the one above, up-to-date, though). The best thing is to actually understand how to find the fresh, new links. Another notable security trick Wasabi uses to verify transactions is the Neutrino protocol. It assigns a task to the client instead of the server, eliminating server-related vulnerability. It has a feature called CoinJoin that combines multiple coins from different users into a single transaction.
Emerging trends shaping darknet marketplaces in 2025—insights into cryptocurrency trading and security. We classify all entities either as sellers or buyers as a function of time. The result is a time series of lists of sellers and buyers for each period and for each market and the U2U network. The classification is performed in five steps (see Fig. 1), as detailed next. Each marketplace is a star-graph where the central node is the marketplace, and the leaf nodes, i.e., the first-neighbors, are the marketplace users. Therefore, all transactions involving the market have the market either as a source or as a destination node.

Once hidden within the depths of the dark web, Torzon Market emerged as a formidable player in the realm of illicit trade. Security professionals express serious concerns about this marketplace due to its unique features and extensive range of illegal offerings. Known for its encrypted communication channels and user-friendly interface, Torzon has attracted a substantial community of buyers and sellers seeking anonymity in their transactions. The market’s growth has raised eyebrows among cybersecurity experts, who fear its potential to facilitate illegal activities on a large scale.
Venture deeper into the underbelly of the dark web, where bustling marketplaces hum with activity and cryptic figures pull the strings. This article unveils the prominent players, explores the vendor ecosystem, and delves into the security measures employed in this digital Wild West. What current policing strategies neglect is that dark web markets are not isolated to the storefronts that are the popular target of crackdowns. These are communities stretched across dark and surface web forums which develop shared tutorials and help one another adapt to any new changes. These closures bind users together and foster a shared resilience and collective experience in navigating these environments.
Future Trends And Predictions For Dark-Web Marketplaces Beyond 2025
Temporal network of multisellers (top) and multibuyers (bottom) between markets for each year. Edges are multihomers, i.e., traders that are simultaneously active in both markets (sellers in the multiseller network, and buyers in the multibuyer network). The width of the edges is proportional to the number of multihomers acting between the markets. These critical changes may not be perceived from macroscopic measures of the ecosystem as a whole.