And within that ocean, the protected dark web provides a secure refuge for illegal activities. Universities and medical providers need to keep confidential content out of the public eye. Website owners often use the robots.txt file to manage traffic and determine what data search engines can access. Cyber hygiene refers to cybersecurity best practices that everyone who actively uses the internet should be implementing to keep themselves and their data protected from common cyber threats. Next, select a dark web search engine like DuckDuckGo that can help you find dark web websites that cannot be indexed by traditional surface web search engines, such as Google or Bing.
Unlike The Deep Web, The Dark Web Is Often Used For Criminal Activity
Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Moreover, the anonymity that protects users can also be a double-edged sword. It comprises just a tiny fraction of the Deep Web, but its potential for misuse makes it a subject of significant concern for security teams and law enforcement.
The next layer is the “deep web,” a large invisible portion of the Internet. We call these websites “deep,” as the content is hidden, and search engines don’t index them. For example, your Web-based email inbox, online banking, checkout and payment pages, and restricted pages, such as website post drafts, company intranets, and government and military databases.
Why Do People Use The Dark Web?

Accessing the TOR network requires a special web browser called a TOR browser. The TOR network allows people to access private, specially encrypted pages ending in ”.onion”. TOR also lets users connect to websites in the surface and deep web anonymously, to prevent internet service providers from seeing what they are browsing. A small, hidden part of the internet accessed via special tools like Tor, often linked to anonymity and sometimes illegal activities, but also used for legitimate purposes like secure communication. Unlike the dark web, which majorly hosts content that is illegal or otherwise restricted in nature, the deep web hosts a wide range of material.
- A subset of the Deep Web, the Dark Web is intentionally hidden from your standard search engines, and is much more difficult to access as all its data is encrypted.
- As accessing the dark web requires a specialized browser, users on the surface/deep web aren’t directly affected.
- Over the centuries, when technology became advanced, humans built machines capable of diving into the depths of the oceans.
- The good news is that there is a much faster version of privacy technology that is similar to Tor, albeit much faster.
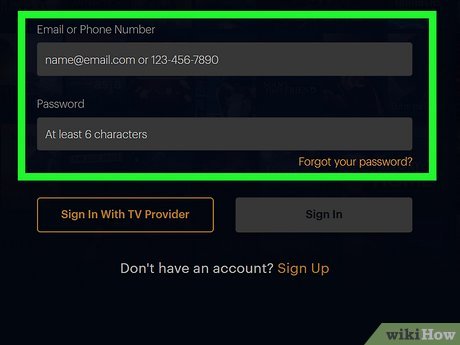
Unlike the dark web, which is deliberately obscured by layers of technology, the deep web exists just below the surface web. The majority of the deep web consists of regular websites that require users to create an account before they can be accessed. As previously mentioned, more than 90% of the traffic on the internet is already on the deep web, so the keys to accessing it safely are virtually the same as the keys to accessing the open web safely. Though you don’t have to perform a penetration test on every website you log in to, you should ensure that it runs on a secure framework that uses HTTPS encryption. Unlike the deep web vs dark web that encompass such secrecy or illegality, this surface web is totally safe to be used daily as well as it falls under more familiar laws and regulations.
Theoretically speaking, it should be impossible to locate dark web servers and track visitors. However, in practice, security flaws in Tor and incorrect server configurations can expose this information to those interested in accessing it. The terms dark web and deep web are perceived to be linked with illegal and otherwise suspicious activity; however, a vast difference exists between the two.
Differences Between The Deep Web And Dark Web
This layer exists to protect sensitive data and ensure that only authorized users can view or interact with certain information. Organizations that monitor dark web activities can detect credential exposure and potential threats before they materialize into breaches. Properly securing deep web resources also prevents unauthorized access to sensitive information. The Deep Web’s design prioritizes privacy, inherently limiting accessibility. Content remains invisible to search engines, requiring users to possess specific credentials or URLs. Using Tor, websites hosted on the dark web can only be viewed by visitors connected to the Tor network.
Accessing The Deep Web Or The Dark Web: Is It Illegal?
It is encrypted and regularly updated, meaning your data won’t be easily accessible to malicious parties. Still, it is critically important to never share any info about yourself with the people you meet and not purchase anything. If you come across software that seems neat and valuable, do not install it. The deep web contains hidden content, such as private databases, government websites, and intranets. These parts of the internet require users to log in to access the data, and they consist of cloud servers that are protected with encryption and unlisted by search engines. Just below the surface web is the deep web, which includes private databases, web pages not indexed by search engines, password protected accounts, and more.
These operational, legal, and ethical issues make clear policies about accessing the dark web are critically important. Security teams (and anyone else tasked with dark web access) should know how to do so safely – and how to report legal queries if they arise. To access the Dark Web safely, use the official Tor browser and consider utilizing a VPN to enhance your privacy by encrypting your internet traffic, preventing tracking by ISPs or government entities. Here are some of the key differences between the deep and dark web. Understanding what the Deep Web and the Dark Web are isn’t just a matter of curiosity—it’s essential for protecting your digital security and making smart decisions online. Greater anonymity allows cyber criminals to do their thing, and the rise of the Bitcoin cryptocurrency which allows incognito payments, has also contributed to illegal trade.
Deep Web Vs Surface Web: What’s The Difference?
This creates a legal risk (possession of harmful images or confidential data). Firstly, we should clarify what is legally permitted when investigating dark web threats. Companies can passively monitor activity and data sales on dark web marketplaces. They detect stolen employee logins, customer data, postal addresses, social security numbers, and other valuable personal data relating to your business operations. Data protection increasingly requires active dark web monitoring to manage compliance risks. To know about the latest cyber threats people fall victim to online, you should keep up with the latest cybersecurity news.
TOR (The Onion Router) Network

The dark web is the traditional place for threat actors to engage in cybercrime through selling stolen credentials, sharing guides for techniques, posting ransomware victims’ information, and more. Visiting a dark web site requires specialized software like the Tor Browser, which routes traffic through a series of random relays across the globe to mask both origin and destination. To access these parts of the internet securely, it is recommended to use privacy-focused browsers like Tor or Brave, and to use a VPN and strong encryption for added security. Many activities on the dark web are illegal, such as the sale of drugs and stolen personal information, while the deep web mostly contains legal but sensitive information. Still, even if it were real or will be real, paying for access is not the way to go.
But contrary to popular belief, not everything found on the dark web is criminal in nature. In fact, some corners of the dark web exist to protect free expression and privacy where such rights are restricted or surveilled. The deep web and the dark web are often confused, but they serve different purposes and have different levels of accessibility. If you go browsing the deep or dark web, you may find plenty of advertisements which claim to offer up the gateway to this hidden corner of the web, in exchange for bitcoins. It’s a well-known scam, so be careful what you click if you go looking for it. Although the company has not disclosed details of the impact, the incident likely dented LinkedIn’s reputation as a trusted platform for networking and professional communication.
The deep web is approximately 400 to 500 times greater than the surface web. The dark web is only a small fraction of the deep web—constituting only 0.01% of it and 5% of the total internet. Despite its depths, not all of the deep web poses a threat; indeed, much of it enhances global knowledge and educates individuals participating in specialized fields. NordVPN is a high-performing VPN we frequently recommend to our readers, and 1Password is a secure password manager we have reviewed in detail. Both of these are excellent utilities you can try without second thoughts. There are many, but my personal favorite is ProtonVPN (free version available).
Deep Web Vs Dark Web: What’s The Difference?
If discovered, automated scanning tools could mark companies as targets for reprisals by criminal groups. These factors make integrating dark web security into your risk management strategy critical. Analysts need security tools to track dark web activities, while engineers must implement alerting systems and controls to counter threats before they escalate. Many dark web sites carry a high legal risk due to illegal activities. Using Tor to browse the dark web is legal, although participation is not advisable.

Hackers may exploit weaknesses in your security setup, leading to unauthorized access to your data and devices. The Silk Road was perhaps one of the most well-known examples of an illegal marketplace in the darknet. It was shut down in 201, but not before it showed the world how easy it was to buy illegal drugs, counterfeit documents, and other questionable items online.